Introduction
Errors that appear without clear context are some of the hardest to resolve in modern software environments. One example is the 2579xao6 code bug, a strange failure pattern that can interrupt stable workflows, break system communication, and leave developers with logs that seem incomplete or contradictory.
If you are investigating the 2579xao6 code bug, this guide explains what it typically means, why it appears, how to troubleshoot it in a structured way, and what teams can do to prevent it from returning. The goal is simple: help you move from confusion to a repeatable fix.
Quick Answer: What is the 2579xao6 code bug?
The 2579xao6 code bug is generally described as an irregular software error identifier associated with unstable runtime behavior, failed process execution, corrupted state handling, or inconsistent dependency interactions.
Unlike common framework errors, the 2579xao6 code bug often appears with:
- Weak or incomplete stack traces
- Little human-readable context
- Intermittent reproduction patterns
- Disruption inside already working systems
- Side effects across modules, jobs, or service calls
In many cases, the error is not the root cause itself. It is a symptom of a deeper issue involving memory, state synchronization, dependency mismatch, malformed input, or environment drift.
Why the 2579xao6 code bug is so difficult to diagnose
The main reason the 2579xao6 code bug frustrates teams is that it often surfaces after a chain of smaller failures.
Instead of pointing directly to one broken function, it may appear only after:
- A background service times out
- A cache returns stale values.
- A module loads the wrong version of a dependency.
- A config variable is missing in one deployment stage.
- A thread or process enters an invalid state.
This makes the 2579xao6 code bug feel random when it is usually conditional.
According to the Accelerate State of DevOps research and industry reliability findings, high-performing engineering teams reduce mean time to recovery by relying on observability, deployment consistency, and fast rollback practices. In practical terms, unusual bugs become easier to trace when systems are instrumented well and release processes are controlled.
What usually causes the 2579xao6 code bug?
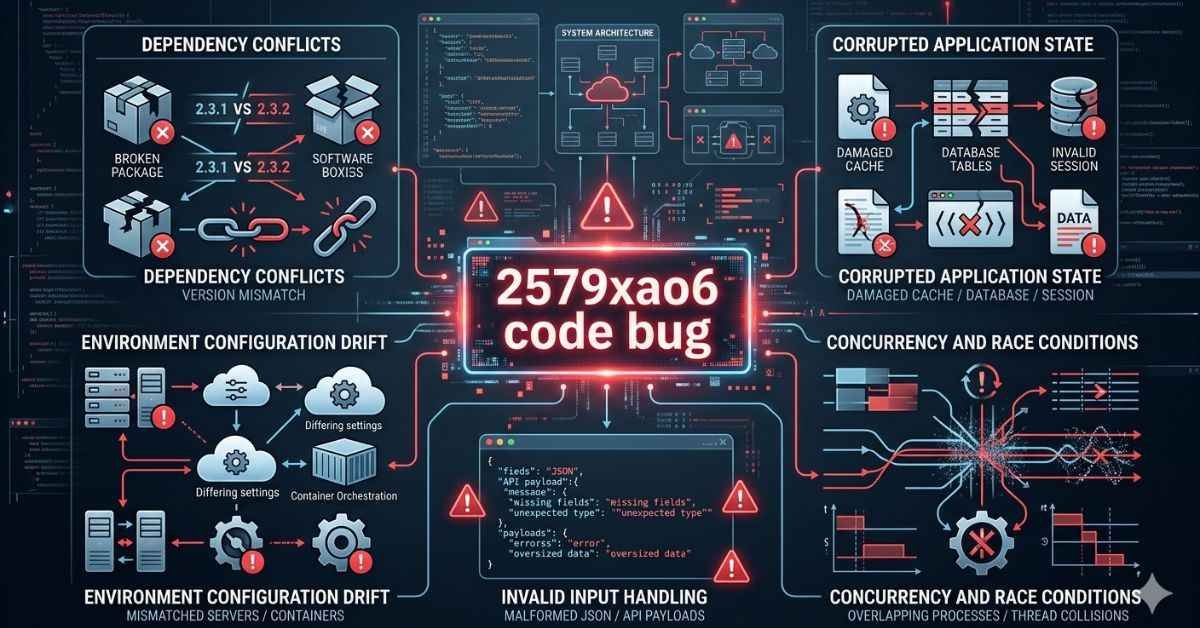
There is no single universal trigger, but several patterns appear repeatedly when teams investigate the 2579xao6 code bug.
Dependency conflicts
A library update may change behavior silently. If one service or component still expects old data structures, error conditions can cascade.
Common signs:
- The bug appears after package upgrades.
- Builds succeed, but runtime fails
- Error frequency differs between local and production environments.
Corrupted application state
Applications that rely on sessions, cached objects, queues, or temporary files can fail when state becomes inconsistent.
This is especially common in:
- Distributed systems
- Multi-threaded applications
- Long-running background workers
- Systems with retries and partial writes
Environment configuration drift
The 2579xao6 code bug may appear only in staging or production because those environments differ in subtle ways.
Examples include:
- Missing environment variables
- Different OS patch levels
- Changed file permissions
- Container image mismatch
- Different database driver versions
Invalid input handling
Some systems fail gracefully with normal malformed input but fail unpredictably when edge-case payloads pass validation and break business logic later.
This includes:
- Null values in nested objects
- Character encoding issues
- Oversized payloads
- Unexpected API field types
Concurrency and race conditions
A race condition can create errors that are hard to reproduce consistently. The 2579xao6 code bug is often reported in systems where multiple operations touch the same resources at nearly the same time.
Symptoms teams notice before the 2579xao6 code bug appears:
Before the 2579xao6 code bug is logged directly, teams often report a few warning signs.
| Symptom | What it may indicate |
| Sudden task failure in stable workflows | Hidden state corruption or dependency issue |
| Partial data writes | Interrupted transactions or timeout chain |
| Random service restarts | Memory pressure, crash loop, or container instability |
| Inconsistent logs across nodes | Distributed tracing gap or environment mismatch |
| Retry storms | Downstream failure not handled correctly |
These symptoms matter because the 2579xao6 code bug is often the visible output of a larger system issue rather than an isolated fault.
How to troubleshoot the 2579xao6 code bug step by step
A structured process is the fastest way to isolate the 2579xao6 code bug.
Capture the exact failure context
Before changing anything, collect:
- Full error message
- Timestamp and time zone
- Service or module name
- Input payload or user action
- Deployment version
- Host, container, or node ID
Without this baseline, the 2579xao6 code bug can become impossible to reproduce later.
Check recent changes
Review what changed in the last 24 to 72 hours:
- Code merges
- Package updates
- Feature flags
- Infrastructure changes
- Database migrations
- Secret rotations
Many unusual software errors are introduced by small operational changes, not major application rewrites.
Compare environments
If the bug appears only in one environment, compare:
- Runtime version
- Installed libraries
- Config values
- Network policies
- Permissions
- Storage mounts
This step resolves a surprising number of 2579xao6 code bug cases.
Reproduce under controlled conditions
Build the smallest reproducible case.
Try to isolate:
- One endpoint
- One function
- One worker process
- One data sample
- One concurrency pattern
If the 2579xao6 code bug disappears in isolation, the root cause may involve orchestration, timing, or integration behavior.
Inspect logs, traces, and metrics together
Do not rely on logs alone.
Use:
- Application logs for exact exceptions
- Metrics for spikes in CPU, memory, retries, and latency
- Distributed tracing for cross-service failure paths
Modern debugging works best when observability signals are correlated rather than viewed separately.
Validate data integrity
Check whether invalid or partially written data triggered the issue.
Look for:
- Broken foreign key relationships
- Null values were not allowed
- Duplicate records
- Queue messages with missing fields
- Cached objects from outdated schemas
Roll back and retest
If the 2579xao6 code bug started after a release, roll back the suspected change and test again.
This does not replace root cause analysis, but it can restore service quickly while your team investigates safely.
Practical fixes for the 2579xao6 code bug
The right fix depends on the trigger, but the following remedies solve many real-world cases tied to the 2579xao6 code bug.
| Root cause pattern | Practical fix |
| Dependency mismatch | Lock versions, rebuild, and test compatibility across environments |
| Invalid state in cache/session | Clear corrupted state and add validation before reuse |
| Missing configuration | Standardize environment variables and deploy config checks |
| Race condition | Add locking, idempotency, or transaction boundaries |
| Malformed input | Tighten validation and reject bad payloads earlier |
| Weak observability | Add structured logging, tracing IDs, and failure alerts |
A good fix should do two things: remove the immediate fault and reduce the chance of silent recurrence.
A realistic case example
A mid-size SaaS team noticed the 2579xao6 code bug appearing in a background billing service after a routine release. The application had passed CI tests, and no obvious code failures were detected in local development.
After investigation, the team found three contributing factors:
- A dependency update changed the serialization format of a queue message.
- One worker node still used an older container image.
- Cached job data allowed partially incompatible payloads to persist for several hours.
The result was intermittent worker crashes and incomplete invoice runs.
The permanent fix included:
- Pinning queue-related package versions
- Forcing immutable deployment artifacts
- Flushing stale cache entries
- Adding schema validation before job execution
- Implementing tracing across queue producer and worker services
This example shows why the 2579xao6 code bug often feels mysterious: the visible error can sit at the end of a multi-step failure chain.
Common mistakes when fixing the 2579xao6 code bug
Teams under pressure often make the issue worse. Avoid these common mistakes.
- Treating the bug code as the root cause
- The 2579xao6 code bug is usually a symptom label, not the underlying problem.
- Restarting services without collecting evidence
- This may temporarily clear the issue while deleting the best clues.
- Debugging only the application layer
- Infrastructure, network policies, container images, and background jobs may all be involved.
- Ignoring intermittent behavior
- If the bug happens “only sometimes,” that is a clue. Timing, state, and concurrency matter.
- Patching production without a rollback plan
- Fast fixes are useful, but untracked hotfixes create more confusion later.
Pro tips to prevent the 2579xao6 code bug from returning
Prevention matters more than emergency recovery.
Use release consistency controls.
Ensure every environment uses the same artifact versions and dependency locks.
Add stronger observability
At minimum, implement:
- Structured logs
- Correlation IDs
- Error rate dashboards
- Trace spans across services
- Alerting for failure spikes
Validate inputs early
Catch bad payloads before they enter business logic or queues.
Harden state management
Use schema versioning for cached objects, sessions, and queued messages.
Test edge cases and concurrency
Many teams test happy paths well but miss timing-related failure conditions.
A 2023 report from IBM on the cost of data-related and operational disruptions reinforces a broader lesson: poor visibility and inconsistent controls increase the impact and duration of technical failures. The same principle applies directly to unusual software bugs.
Related technical areas worth checking
When investigating the 2579xao6 code bug, it helps to review nearby failure domains:
- Runtime exception handling
- API contract validation
- CI/CD deployment integrity
- Container drift and image versioning
- Database transaction behavior
- Cache invalidation strategy
- Queue processing guarantees
- Thread safety and async task coordination
These connected areas often reveal the real cause faster than focusing on the error code alone.
FAQs
What does the 2579xao6 code bug mean?
It usually refers to an unusual software error state linked to runtime instability, invalid state handling, environment mismatch, or dependency conflict rather than one standard documented framework issue.
Is the 2579xao6 code bug caused by malware?
Usually no. In most cases, it is tied to application logic, system state, deployment inconsistency, or integration failure. However, security review is still wise if the error appears with unauthorized changes.
Why does the 2579xao6 code problem show up at random?
It often depends on timing, cached state, concurrency, or specific input conditions. That makes it look random even when it follows a hidden pattern.
Can clearing the cache fix the 2579xao6 code bug?
Sometimes. If a stale or corrupted state is involved, clearing cache, sessions, or temporary storage can help. But this should be done only after capturing logs and context.
How do I reproduce the 2579xao6 code bug?
Start with exact timestamps, payloads, deployment versions, and system conditions. Then isolate the smallest workflow that triggers the issue and test under controlled conditions.
Is the 2579xao6 code bug a backend-only issue?
No. It may originate in frontend input handling, API contract mismatch, middleware transformation, worker queues, or database state. The visible error may surface in the backend, but the cause can begin elsewhere.
What is the fastest safe response in production?
Capture evidence first, assess user impact, compare recent changes, and roll back suspected releases if needed. Then perform root cause analysis before redeploying a permanent fix.
Conclusion
The 2579xao6 code bug is difficult not because it is magical, but because it usually appears at the end of a deeper chain of failures. That chain may involve dependency conflicts, corrupted state, environment drift, malformed input, or concurrency problems.
The best way to solve it is methodical: capture context, compare environments, reproduce the issue, inspect observability data, validate state, and apply a fix that also reduces recurrence.
If your team treats the 2579xao6 code bug as an isolated mystery, it will keep coming back. If you treat it as a signal of system-level weakness, you can fix both the incident and the process that allowed it.
Visit the rest of the site for more interesting and useful articles.